==Introduction to IT Governance==
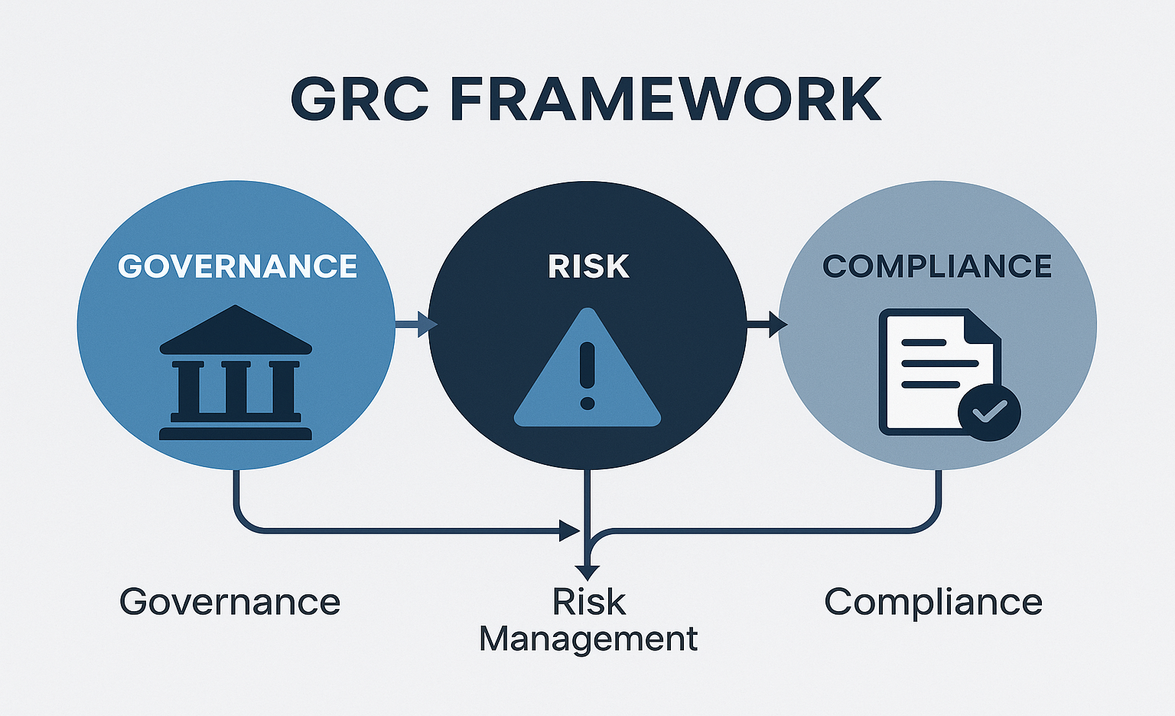
IT governance is the framework that ensures an organization’s information technology (IT) supports and aligns with its business goals. It involves defining clear roles, responsibilities, and processes to manage IT resources effectively, mitigate risks, and maximize value.
!
Choosing a Cybersecurity Framework: Key Considerations
Selecting a cybersecurity framework is not a one-size-fits-all decision. Organizations must evaluate multiple factors to ensure the framework aligns with their unique needs and goals: