GRC Framework
==G.R.C. Governance, Risk, Compliance==
G.R.C. compliance ensures that IT aligns with business goals, manages risks and meets compliance requirements.
!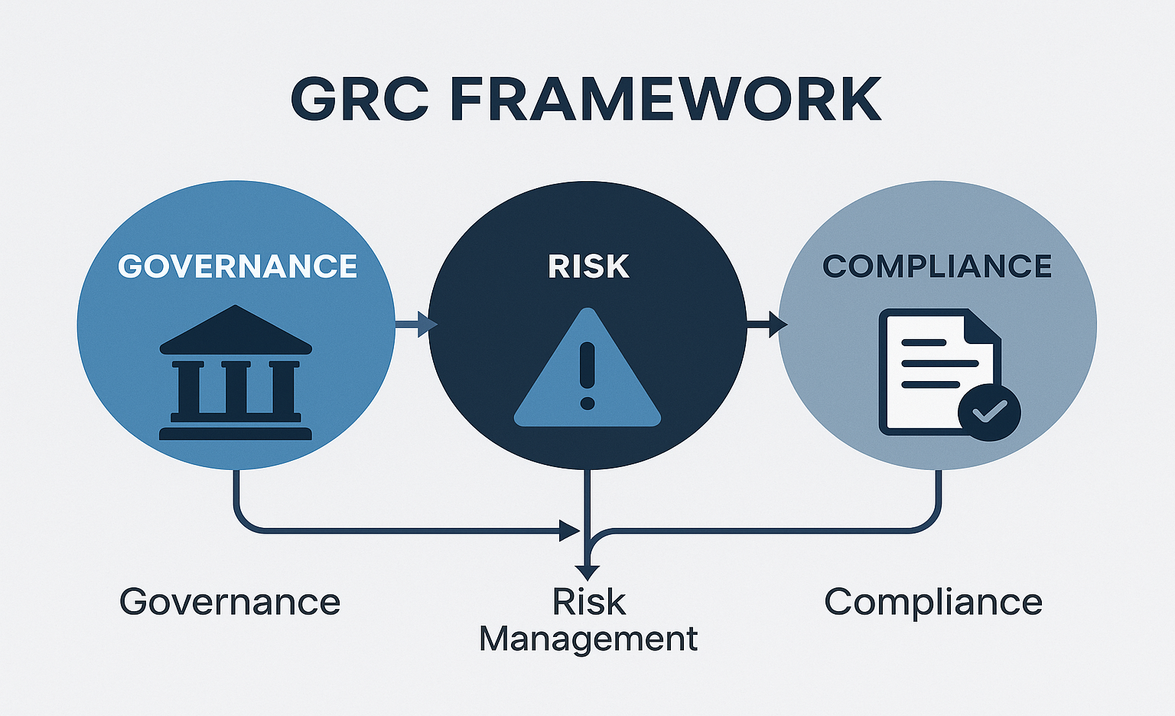
Governance: involves setting policies and procedures, guiding how to operate and make decisions, defining goals, assigning roles, ensuring actions align with the mission and values and promoting accountability, transparency, and ethical behavior. Risk management: identifies, evaluates, and addresses threats such as financial uncertainties, cybersecurity threats, operational issues, and regulatory non-compliance. It minimizes the impacts of unexpected events, protects resources, enables smooth operations, and supports decision-making. Compliance: entails following relevant laws, regulations, standards, and policies. It ensures the organization operates legally, enhances reputation, credibility, and trust, and helps avoid legal problems and obtain necessary certifications and licenses.
==Benefits and Limitations of G.R.C.==
==Benefits of G.R.C.==
It integrates separate management into a unified approach:
- Reduced Cost: Streamlines operations, eliminates redundant and disconnected processes, resources, and tools.
- Enhanced Security: Provides visibility into risks, threats and vulnerabilities. Helps secure infrastructure.
- Improved Compliance: Ensures organizations maintain ongoing compliance and avoid potential legal and regulatory issues.
- Protection from Penalties: Protects from adverse audits, penalties, and legal actions.
- Risk Reduction: Reduces risks across organizations: business, financial, operational and security.
- Operational Efficiency: Enables quick and accurate information gathering, decreases duplication of efforts and automates routine tasks and workflows.
- Transparency and Accountability: Helps build trust with stakeholders and promotes accountability and ethical behavior.
Limitations:
G.R.C. is valuable but requires customization, ongoing updates and strong organizational buy-in to be effective.
==GRC Components==
Guidelines, Policies, and Standards:
- Policies: Acceptable Use Policies (AUP), Information Security Policies, Business Continuity Plans, Disaster Recovery Plan, Incident Response Plan.
- Standards: Password standards (e.g., 12 characters), Multi-Factor Authentication (MFA), Physical Security, Encryption (SSL/TLS and AES).
- Procedures: Change Management Procedures, Onboarding and Offboarding Protocols, Comprehensive Playbooks.
- Additional Considerations: Legal requirements, industry best practices, regulatory compliance, and G.R.C. strategy to comply with laws and regulations and align with external and internal factors.
==GRC Structures==
Boards for strategic direction and supervision, committees for targeted approaches and in-depth management and supervision, government entities to protect public interest.
GRC Tools:
MetricStream, RSA Archer Suite, IBM FIRST Risk Case Studies, and IBM OpenPages with Watson.