NIST Framework CSF 1.1
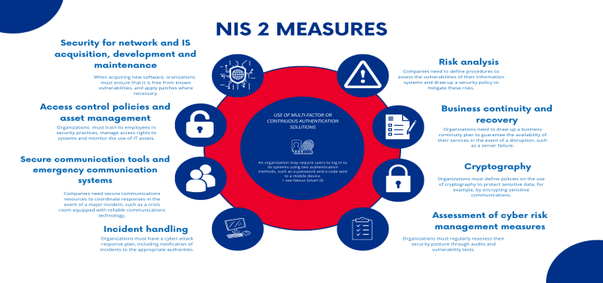
==Network and Information Security (NIS2)==
NIST Framework CSF 1.1 overview:
The NIST framework Core consists of:
- Govern, Identify, Protect, Detect, Respond, and Recover as functions and 108 subcategories.
The NIST framework Tiers consists of:
- Tier 1 (partial): Informal, reactive processes.
- Tier 2 (Risk-Informed): Approved policies, risk management.
- Tier 3 (Repeatable): Formalized processes, risk integration.
- Tier 4 (Adaptive): Continuous improvement, dynamic adaptation. The NIST framework Profiles consists of:
- Current Profile: Assesses existing cybersecurity practices.
- Target Profile: Defines desired cybersecurity outcomes.
- Gap Analysis: Compares profiles to prioritize improvements.
Purpose: Align cybersecurity with business goals and enhance resilience.
- Govern: create cybersecurity policies, direct choices about stakeholders’choices, safeguard the organization’s mission, describe security goals, devise a cybersecurity plan, control supply chain risks and supervise the cybersecurity strategy.
- Identify: understand cybersecurity risks, recognize risks associated with the organization’s assets (systems and data), aid actions for the organization’s risk strategy, and improve policies and procedures.
- Protect: use security measures to mitigate cyber threats, safeguard the organization’s assets, implement security measures such as controlling access rights and permissions, creating awareness, ensuring data security, protecting hardware and software, and ensuring IT infrastructure resilience.
- Detect: identify potential cyberattacks and recognize signs of cyberattacks.
- Respond: prepare a response to discovered cybersecurity incidents, analyze, mitigate, manage, report, and communicate the effects of cyber incidents even with third parties.
- Recover: Restore assets and operations affected by cyberattacks and normalize to reduce the impact of cyberattacks.
==NIST CSF Function==
- Connects all components, enables quick identification, handling and resolution, develops and tests plans, and safeguards components.
!
==Compliance and Legal Considerations==
- Security Compliance: crucial for ensuring necessary standards and regulations are met to protect data, assets, and reputation. Influenced by external factors such as government regulations and market dynamics.
- Regulatory Requirements: includes mandated laws, regulations, and guidelines to safeguard sensitive information, maintain industry standards, and protect consumer rights. G.D.P.R. mandates guidelines for data protection and privacy.
- Legal Considerations: understand legal implications, protection against lawsuits, ensure compliance with intellectual property laws, and adherence to employment regulations.
==Monitoring Compliance==
- Due Diligence: investigate and validate security posture and threats, analyze the security landscape, assess vulnerabilities, and ensure protective measures are updated.
- Attestation and Acknowledgement: attestation involves witnessing and verifying authenticity, confirming the functioning of security controls. Acknowledgement involves recognizing and admitting the truth or existence and accepting and addressing security breaches.
- Automation: uses technology to perform tasks, streamlines security operations, and enhances efficiency. Leverage AI and ML for threat detection and response, reduce manual workload, and focus on strategic initiatives.
==Standardized Processes and Automation==
-
Standardized Processes: standardize processes to identify, evaluate, and manage cyber threats. This includes network configuration and management, access control and identity management, vulnerability and patch management, incident response and recovery, and continuous improvement training.
-
Automation and Orchestration: resource provisioning, Role-Based Access Control (RBAC), security groups, ticket creation, escalation, enabling/disabling services and access, continuous integration and testing and integrations and APIs.